By: Benjamin Sugg, CNA
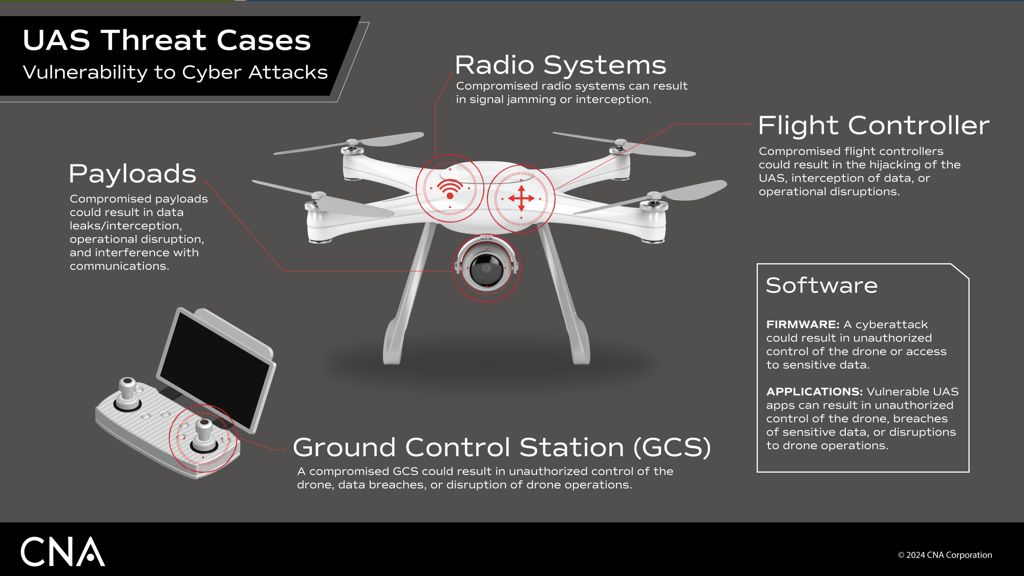
In modern conflicts,unmanned aircraft systems (UAS) have proven pivotal and, as such, continue to redefine military strategy. In the Ukraine conflict, for example, UAS cybersecurity vulnerabilities have been exploited to intercept communications, manipulate GPS signals and in some cases seize control of the drones themselves. As the U.S. increasingly integrates UAS into its own operations, securing the software supply chains behind these systems to ensure resilience against emerging threats has become a national imperative.
As part of that effort, Software Bills of Materials (SBOM) provide detailed inventories of software components and their dependencies to enable better management of vulnerabilities and compliance with evolving regulatory standards. Despite their growing importance, SBOM adoption within the UAS ecosystem remains limited due to industry fragmentation, technical barriers and a lack of regulatory drivers. To address these challenges, CNA has developed the Vulnerability Intelligence for Software and Trusted Assets (VISTA) tool. VISTA generates SBOMs containing vulnerability data and visualizes those vulnerabilities through an intuitive graph-based interface that provides a clear view of the user’s software security posture across their UAS fleets to provide actionable information for remediation of compromised components. VISTA demonstrates how SBOMs can contribute to the advancement of the wider supply chain risk management process, improve software security and support compliance for UAS manufacturers, operators and regulators.
Who We Are, What We Do
CNA is an independent, not-for-profit research and analysis organization dedicated to solving complex challenges for the U.S. government. Our Cyber Research Program provides objective analysis on cybersecurity principles, regional strategies, workforce organization and emerging technologies to military leaders, policymakers and industry stakeholders.
In the civilian sector, CNA has supported the Federal Aviation Administration (FAA) for over 30 years in modernizing air traffic management and preparing for new entrants into the National Airspace System (NAS), including UAS and Advanced Air Mobility (AAM). CNA has supported the development of the FAA’s UAS Traffic Management (UTM) security requirements, including the application of the zero trust architecture and has partnered with NASA’s Urban Air Mobility (UAM) team to conduct research and analysis focused on the cybersecurity needs of the UAM ecosystem, such as blockchain applications.
The Complex Origin of UAS Components
The supply chain for commercial UAS remains highly complex. Multiple vendors contribute to critical systems such as flight controllers, communication protocols and mission-specific applications. These interconnected software components create dependencies that can be difficult to track, which increases the risk of vulnerabilities.
A real-world example includes the CVE-2020-10282, where the MAVLink protocol used in commercial and open-source ground control stations (GCS) was found to lack authentication in v1.0. This enabled spoofing, unauthorized command injection and man-in-the-middle attacks. The implementation of an SBOM in this use case would have identified the vulnerable MavLink libraries being used by the GCS platforms and provided visibility into which platforms were exposed.
Why SBOMs Matter for UAS
An SBOM is a formal record of the components and supply chain relationships within software. For UAS, which integrate software and hardware from multiple vendors, SBOMs help address the complexity of dependencies and vulnerabilities.
Without SBOMs, organizations often rely on manual tracking or incomplete documentation of software components. This leaves critical dependencies and vulnerabilities unaccounted for. This approach introduces significant risks, including hidden vulnerabilities, potential compliance gaps and supply chain attacks.
Conversely, the primary benefits of implementing SBOMS include:
- Vulnerability Management: SBOMs allow organizations to identify and assess vulnerabilities within UAS software components.
- Software Provenance: SBOMs ensure that only trusted and verified software is integrated into UAS systems.
- Operational Efficiency: While the initial adoption of SBOMs may seem like an additional task at first, they ultimately improve long-term operational efficiency by automating and streamlining processes that would otherwise be manual, error-prone or incomplete.
- Improved Cybersecurity Regulatory Requirements: Early SBOM adoption supports compliance readiness for evolving regulations in UAS airworthiness.
Understanding Delays: Barriers to SBOM Adoption
Although SBOM adoption is growing in industries like automotive and healthcare, the UAS sector faces unique challenges. Unlike automotive and healthcare sectors, which benefit from more standardized frameworks and mature development practices, the UAS industry’s fragmentation spanning recreational, commercial and government-operated platforms creates inconsistent adoption of SBOMs due to varying software maturity and limited standardization among smaller manufacturers.
While federal agencies like the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) and the FAA have published advisories, binding requirements for SBOM generation are lacking. Without established compliance requirements, industry will likely adhere only to minimal standards. This limits progress toward widespread adoption
Current tools also lack intuitive visualization capabilities. This makes SBOM data difficult to interpret. Finally, smaller manufacturers and operators often lack the financial and personnel resources to implement SBOM practices at scale.
CNA designed the VISTA tool to overcome these barriers by automating SBOM generation, integrating vulnerability data, and providing user-friendly visualization.
VISTA : Detecting and Visualizing UAS Vulnerabilities
The VISTA tool provides an intuitive user interface that allows SBOMs to be quickly generated and scanned for vulnerabilities.
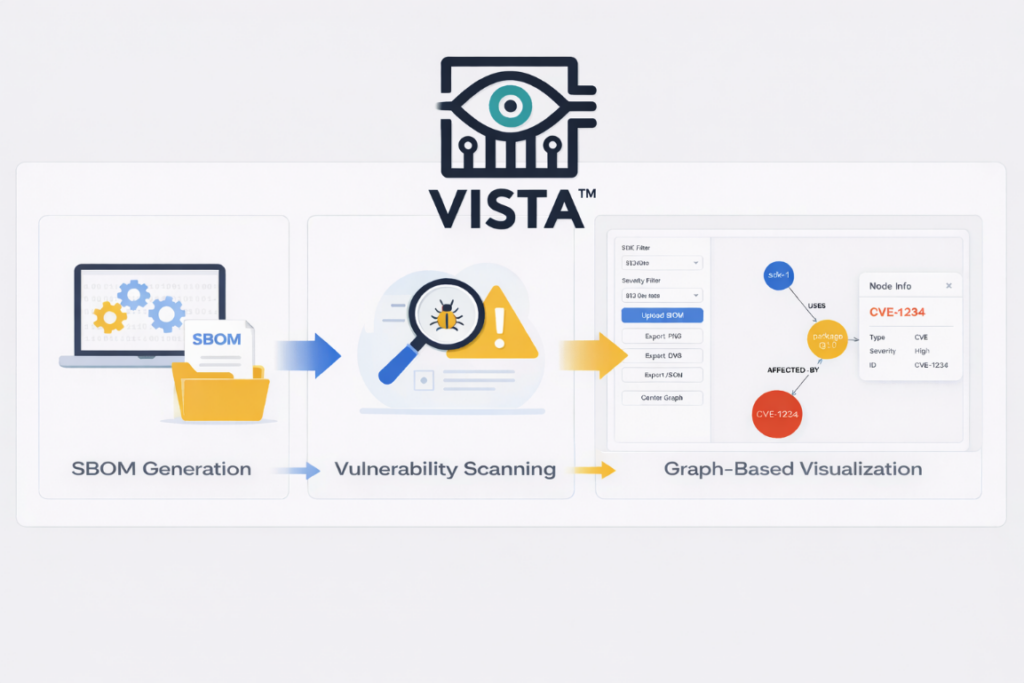
Here’s how it works. It generates the SBOM using Syft, an open-source command-line interface (CLI) tool, VISTA generates SBOMs from container images and file systems. Then it scans for vulnerabilities using Grype, another CLI tool that works in conjunction with Syft to scan the generated SBOMs for known vulnerabilities and produce CycloneDX-compliant SBOMs containing critical vulnerability data. Finally, it imports SBOM data into a graph database. This enables interactive visualization of component relationships, dependency hierarchies and vulnerability propagation.
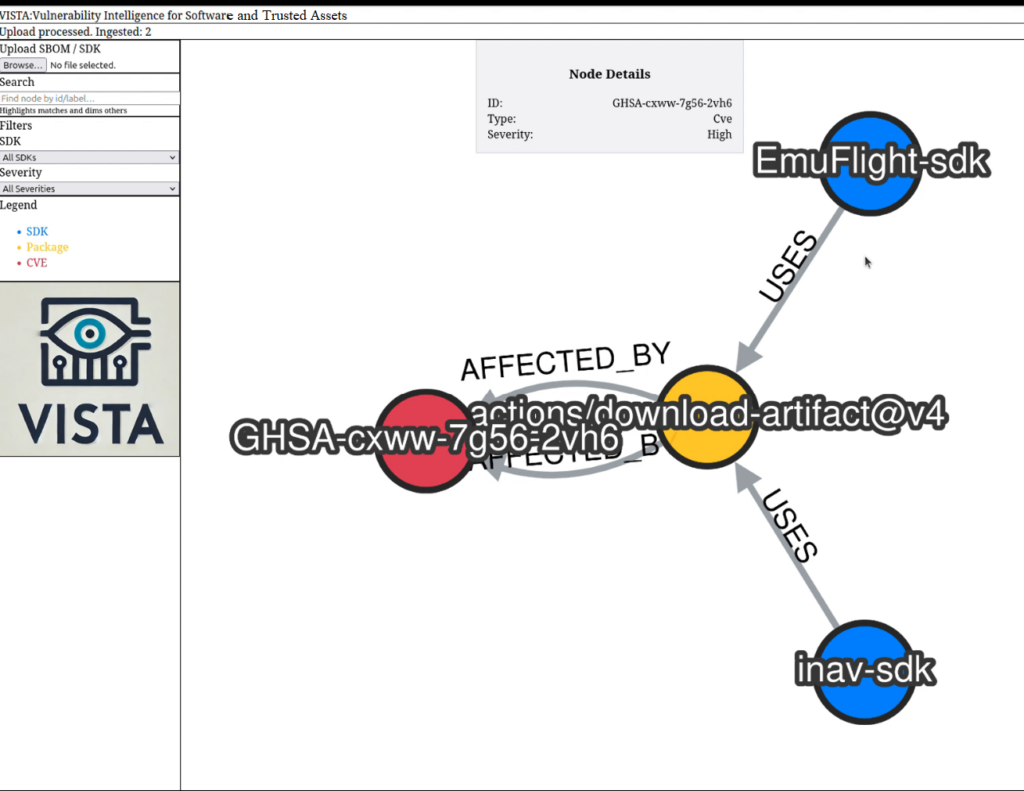
Users can filter by severity, search by component, and assess dependencies affected by Common Vulnerabilities and Exposures (CVEs). Specifically, users can investigate the relationships between components such as software development kits (blue), software packages (yellow), and identified vulnerabilities (red).
The visual mapping of these nodes provides greater insight into the scanned system’s security posture to aid the remediation process. The image below provides an example of how the same vulnerable software package was identified in two unassociated flight controller SDKs, highlighting the issue of known vulnerabilities that may exist across platforms and vendors.
Advancing SBOM Adoption in UAS, More VISTA on the Horizon
As the implementation of SBOMs continues to grow, the UAS sector must overcome adoption barriers to secure its complex software supply chains. VISTA demonstrates how SBOMs can be integrated efficiently into existing workflows to support compliance readiness and improve risk management.
By addressing challenges like fragmentation, tooling limitations and resource constraints, the VISTA tool benefits manufacturers, operators, regulators, and industry associations by enabling streamlined SBOM generation, vulnerability analysis and compliance workflows. Manufacturers can integrate SBOMs into development pipelines. Operators use them to assess procurement risks. Regulators gain tools to define SBOM baselines and certification standards. Industry associations can support adoption through tailored frameworks and collaborative exercises.
Building on the success of the VISTA prototype, CNA aims to expand the tool’s capabilities to offer a more robust solution for vulnerability tracking and lifecycle management. Future enhancements will focus on refining the graphical user interface (GUI) and optimizing the user experience to ensure seamless integration into existing workflows. These improvements will enable stakeholders to more effectively manage software security and compliance across the UAS ecosystem.

